The Real Cost of Ransomware for SMBs: Budgeting, Insurance, and Recovery Strategies in 2025
If you’re a CIO, CTO, CISO, CEO, CFO, IT Director, or Managing Partner at a small or mid-sized business in law, architecture, finance, or energy, you’re already aware: ransomware is not an “if,” but a “when” scenario. What keeps leaders like you up at night isn’t just the threat itself—it’s the chilling uncertainty of how much a single breach could cost, how to budget honestly for risk, what insurance really covers in 2025, and whether your teams could bounce back fast enough to protect your reputation and bottom line.

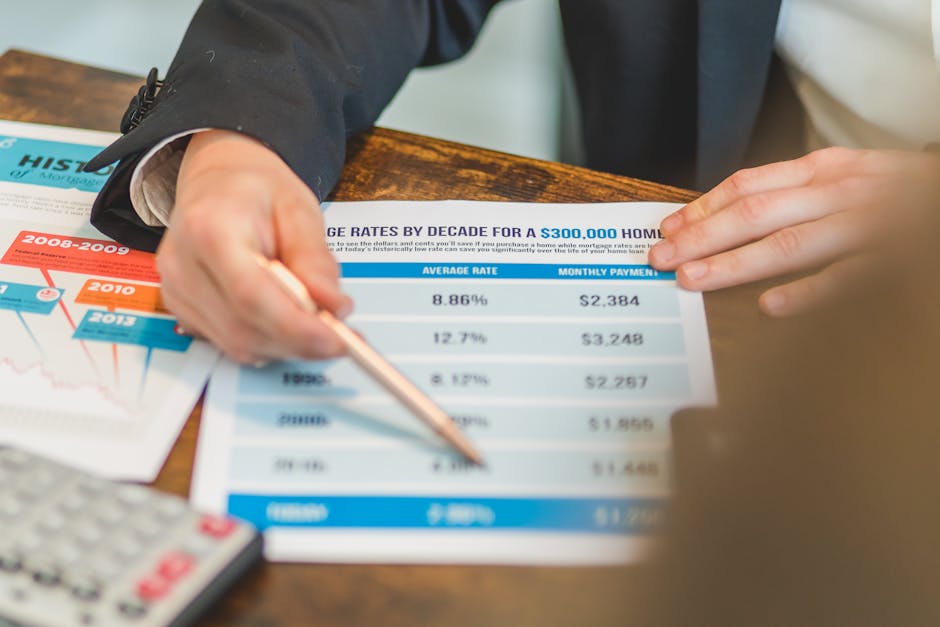
The True Price Tag of Ransomware for SMBs in 2025
Every headline seems to tout yet another sky-high ransomware figure. But for most SMBs, especially those in regulated sectors like law and finance, the biggest surprise is the compound effect: it’s not just ransom money. It’s downtime, lost billable hours, delayed projects, compliance headaches, lost client trust, and—if you’re especially unlucky—the fine print in your cyber insurance policy refusing to pay out when you need it most.
- Average direct cost to recover: Well over $250,000 for SMBs (2025 estimates)—that’s not including soft costs or opportunity loss.
- Typical downtime: Most SMBs lose at least 5 days of critical operations. In law and finance, this could mean missing court deadlines or regulatory filings.
- Revenue impact: Over 40% of SMBs lose clients, and nearly half lose significant revenue after a serious ransomware incident.
- People drain: The median attack ties up 15–20 team members—many with little-to-no formal cyber incident training.
- Hidden exposure: Legal, regulatory, forensic, and notification costs can quietly double your final bill.

Why Your Firm Is the Perfect Target (and Not by Accident)
SMBs are now ground zero for ransomware. No, it’s not just luck of the draw. Attackers are actively researching industries where:
- IT teams are overstretched or part-time
- Valuable data—think legal documents or wire transfer instructions—can never go public or be lost
- Compliance fines are steep and deadlines non-negotiable (try explaining a ransomware delay to a regulator!)
- Bigger partners rely on your business as a supply chain gateway
Put simply: You have resources, reputation, and urgency—but not a Fortune 500 IT war chest.
Budgeting for Ransomware: A Smart Leader’s Playbook
It’s tempting to hope “good enough” security and annual insurance will cut it. But in 2025, the smart play is a layered—and painfully realistic—budget. In our experience at Bonelli Systems, this means targeting your spend to the biggest risk and business-recovery levers:

Five Steps to Building a Ransomware-Ready IT Budget
- Inventory core business assets: Know which servers, laptops, and data sets are mission-critical (for a law firm, think e-discovery databases; for architecture, design IP or project files).
- Layered security for endpoints: Budget for tools that watch for odd behavior on user computers and servers (think of Endpoint Detection and Response as a digital hall monitor—smart and tireless).
- Immutable and offsite backups: Daily backups stored so they can’t be overwritten by attackers (cloud or physical isolation). True story: firms with these can say “no, thanks” to ransom notes.
- Security awareness training: Because ransomware often starts with a single email click. (Especially critical for firms with rotating admin staff or interns.)
- Incident response agreements: Pre-arrange who you’ll call—from internal teams to external partners—when things go sideways. Yes, actually write out the emergency plan.
Quick cost reality check: A typical 50-person SMB in 2025 should expect to budget $10,000–$60,000/year for layered defenses. Cyber insurance for $1M of coverage is now $1,500 at minimum—often much more for law or finance.
Cyber Insurance in 2025: What’s Covered, What’s Not
Let’s address the elephant in the server room: Cyber insurance is a must for regulated sectors, but it’s no longer a magic get-out-of-jail-free card. Here’s the honest 2025 rundown:
- Underwriting is stricter than ever: Insurers demand hard evidence of patching, multi-factor authentication, and incident response plans—especially for law and finance firms. Miss a box? Claim denied.
- Coverage carveouts are the norm: Nation-state attacks, gross negligence, or lack of tested backups can leave you holding the bill.
- Premiums are rising fast: $1,500–$6,000 per $1M of coverage is the new normal for higher-risk industries.
- Compliance counts twice: For law and financial services, a weak compliance record can both raise premiums and complicate regulatory reporting after an attack.
Pro tip: Always review insurance annually with your IT and legal teams. Changes in systems—like adding cloud services or remote work—can easily void policy conditions if not documented.
Recovery in Action: What to Do (and Not) When Ransomware Strikes
The moment of truth isn’t the attack itself—it’s your first 2–4 hours of response. Think of it as your “digital fire drill.” Here’s a step-by-step recovery list:
- Detect, isolate, and stop the bleed: Use advanced endpoint security to automatically find and quarantine infected systems instantly (before ransomware spreads like wildfire).
- Disconnect at-risk systems from networks—fast! (Treat it like a real building fire: keep it from spreading.)
- Activate your incident response plan: This is not the day to “wing it.” Your playbook should spell out what to do, who to call, and in what order.
- Engage legal, compliance, and your MSSP: Law and finance especially—they need documentation for notifications and client updates.
- Wipe and rebuild only from trusted backups: Accept nothing less than immutable or offline versions. This is where all previous investments pay off.
- Communicate, document, disclose: Don’t hide an incident—clients and regulators will thank (and trust) you for transparency.
Industry-Specific Ransomware Challenges (2025)
Law Firms
- File exposure: Client and case documents are often “irreplaceable”—and public release means professional ruin or malpractice.
- Compliance timelines: ABA, state bar, and GDPR set strict incident disclosure rules—delays, even by hours, increase risk.
Finance & Investment
- Transaction integrity: Wire fraud and regulatory sanctions are common after a breach. Expect the SEC and clients to be watching.
- Audit requirements: SOX, FINRA, and payment processors now routinely demand proof of incident response and backup integrity.
Architecture & Energy
- Critical supply chain risk: A ransomware hit on your BIM/CAD files or grid operations can interrupt major construction projects—or even endanger public safety.
- Insurance exclusions: Many insurers require documented supply chain protections—and reserves for downtime losses not covered.

Proactive Security Tips: Building Resilience for 2025
- Embrace multifactor authentication everywhere: It’s not just a “nice to have”—it’s the top reason claims get paid vs. denied.
- Automate patching and critical updates: Every week missed is a door left open. Consider managed IT services if your team already wears too many hats.
- Invest in user-friendly, regular training: The best security tech is useless if your people don’t recognize a phishing email.
- Test backups and recovery quarterly: If no one has willingly restored from backup twice a year, treat your backups as broken until proven otherwise.
- Simulate real-world attacks: Every sector is targeted differently (phishing in law, spear attacks in finance). Practicing for your reality—think drills, not just policies—makes all the difference.
Your Next Steps: Don’t Face Ransomware Alone
The worst day to figure out a ransomware plan is the day your firm gets the ransom demand. Investing now—in layered protections, incident response planning, and insurance review—pays off tenfold in cost avoidance and peace of mind. At Bonelli Systems, our team draws on direct experience supporting legal, financial, and energy-sector SMBs through the cyber gauntlet.
Ready to see where your real risks and budget blind spots are? Start by booking a free, zero-obligation risk assessment with our experts:
https://bonellisystems.com/contact-us/
Stay secure. Stay prepared. And remember—ransomware respects no one’s schedule or budget, but a proactive response puts you back in control.











